Splunk Attack Analyzer Dynamic Analysis
Description
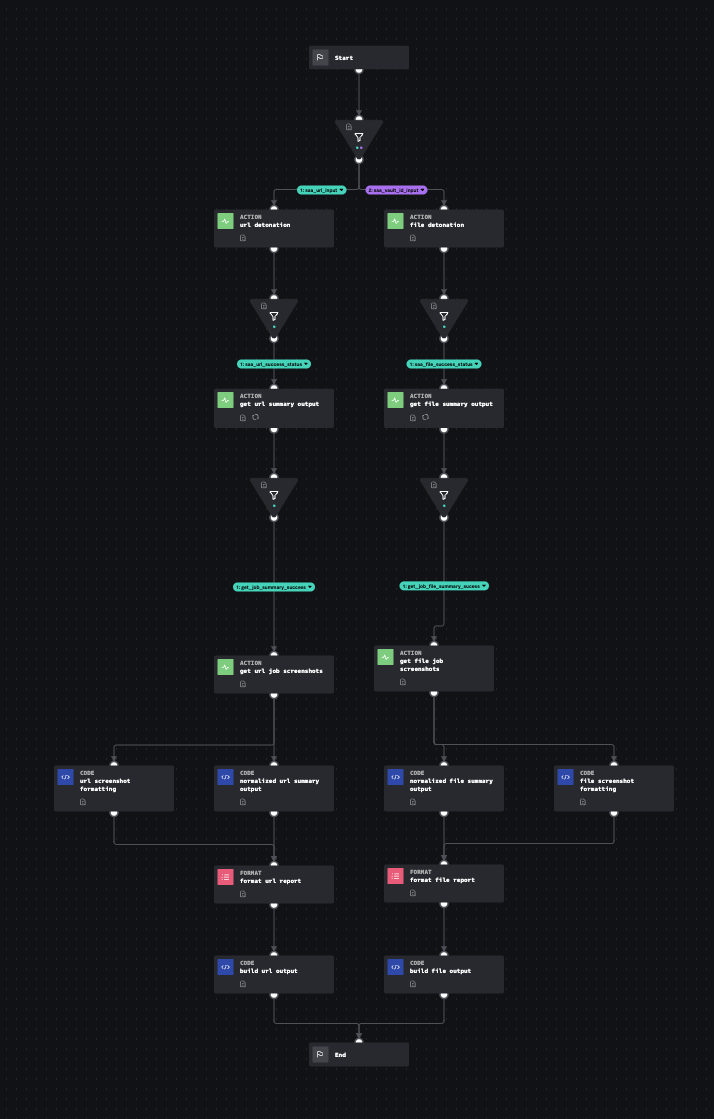
Accepts url link, domain or vault_id (hash) to be detonated using Splunk Attacker (SAA) API connector. This playbook produces a normalized output for each user and device.
- Type: Investigation
- Product: Splunk SOAR
- Apps: Splunk Attack Analyzer Connector for Splunk SOAR
- Last Updated: 2023-03-24
- Author: Teoderick Contreras, Splunk; Kelby Shelton, Splunk
- ID: c77faffe-1339-43b0-b870-86582da9063e
- Use-cases:
- Enrichment
- Phishing
- Endpoint
Associated Detections
How To Implement
This input playbook requires the SAA API connector to be configured. It is designed to work in conjunction with the Dynamic Attribute Lookup playbook or other playbooks in the same style.
D3FEND
| ID | Technique | Definition | Category |
|---|---|---|---|
| D3-DA | Dynamic Analysis | Executing or opening a file in a synthetic "sandbox" environment to determine if the file is a malicious program or if the file exploits another program such as a document reader. | File Analysis |
Explore Playbook
Required field
Reference
source | version: 1