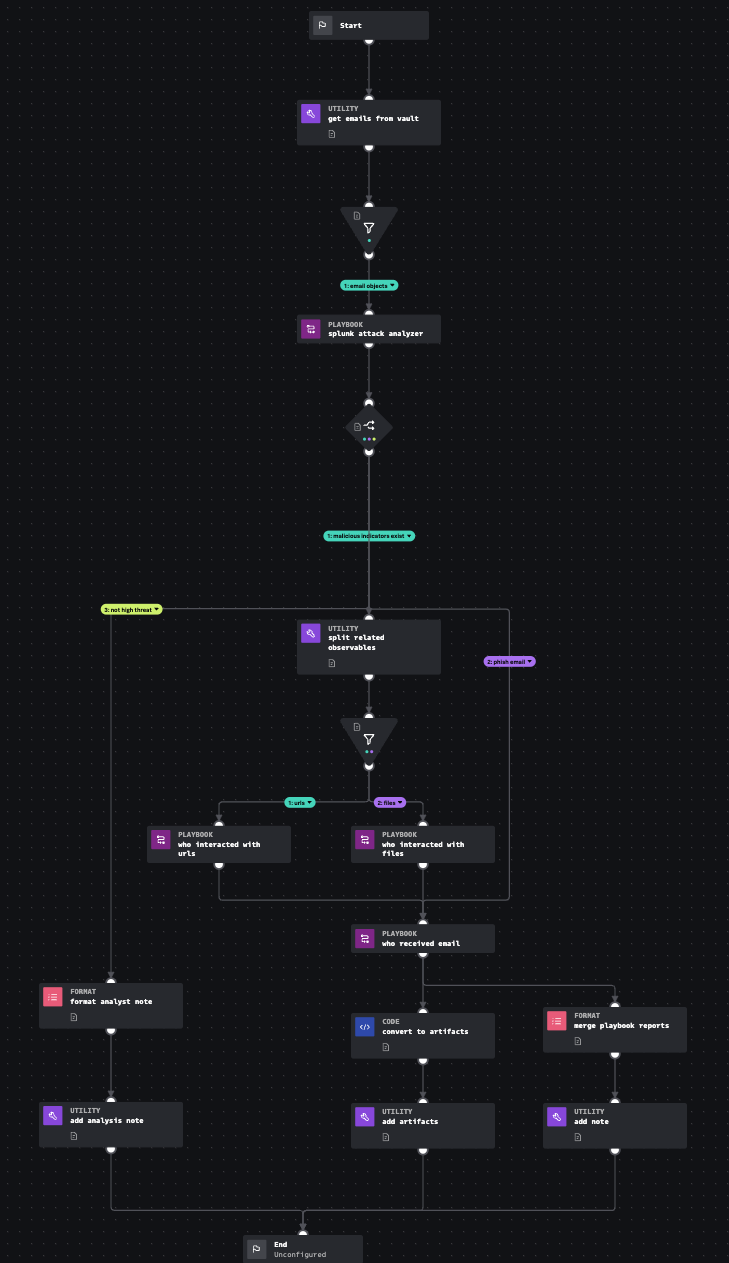
Splunk Automated Email Investigation
Description
Leverages Splunk technologies to determine if a .eml or .msg file in the vault is malicious, whether or not it contained suspect URLs or Files, and who may have interacted with the IoCs (email, URLs, or Files).
- Type: Investigation
- Product: Splunk SOAR
- Apps:
- Last Updated: 2023-12-23
- Author: Kelby Shelton, Splunk
- ID: c69e3310-a819-4d16-a615-348fa8d88b0b
- Use-cases:
- Phishing
Associated Detections
How To Implement
Ensure the four input playbooks are loaded onto the system. The input playbooks are designed to be swappable within the same category (e.g., Message Activity Analysis) with minimal to no changes downstream.
D3FEND
| ID | Technique | Definition | Category |
|---|---|---|---|
| D3-DA | Dynamic Analysis | Executing or opening a file in a synthetic "sandbox" environment to determine if the file is a malicious program or if the file exploits another program such as a document reader. | File Analysis |
| D3-SRA | Sender Reputation Analysis | Ascertaining sender reputation based on information associated with a message (e.g. email/instant messaging). | Message Analysis |
Explore Playbook
Required field
Reference
source | version: 1